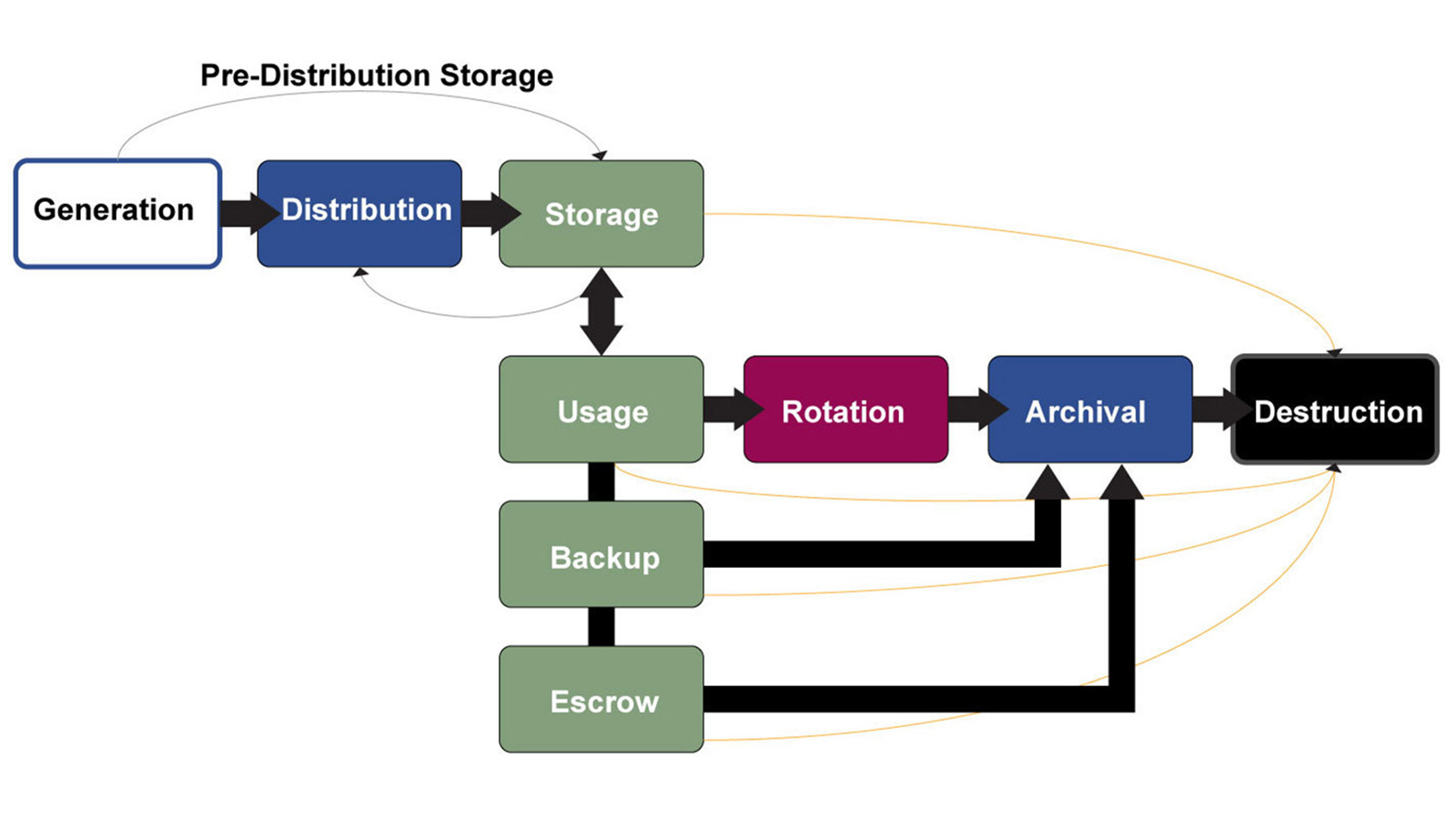
The KEES Key Exchange Service supports organizations with all aspects of the full key management lifecycle, as depicted below.
Key Management Lifecycle
KEES Common Use Cases:
- Cryptographic Subject Matter Expertise
- Key Management Staff Augmentation
- Hardware Maintenance
- Back-Up/Archive Storage
- Outsourced Compliance
- Mass Key Generation & Distribution
- Key Inventory Escrow
- Key Inventory Rotation
- Remote Key Loading
- Virtual HSM Technology
- Internet of Things
eKMS as a Service
With the expansion of encryption requirements for any enterprise today, the requirement to maintain a centralized key management utility or team is more necessary than ever before. Still, many organizations struggle to find and dedicate full time subject matter experts and technologies to manage this growing requirement. The GEOBRIDGE KEES key exchange service closes this gap.
By utilizing the KEES eKMS as a Service offering, organizations benefit from our full-time and dedicated staff subject matter expertise for the purposes of key generation, key distribution, key rotation, key escrow, and compliance scope reduction.
eKMS as a Service will manage and perform the full key management lifecycle on your behalf.
HSM as a Service
While the vast majority of organization’s technical infrastructure is migrating to cloud based services, HSM technology does not lend itself to this strategy quite so easily. The primary purpose of HSM technology is to ensure that cryptographic keys remain protected, not only in storage, but also while in use. Virtual solutions are software by definition, but HSMs are required to be hardware. Moreover, most HSM technology leverages proprietary APIs and rely on externally protected key stores.
The KEES platform is the ideal bridge between hardware requirements and the quest for virtual HSM technology. By leveraging cryptographically segregated relationship structures, the KEES platform extends a simple JSON schema RESTful API for remote access to a dedicated clients protected key store. Connections are supported over TLS 1.2. From there, the KEES platform translates the inbound RESTful API to many different proprietary APIs for various HSM manufacturers including Thales, Safenet, Utimaco and Atalla.
HSM as a Service eliminates the requirements of hardware management, offers dramatic compliance scope reduction, and utilizes full-time staff professionals to perform sensitive key management functions.
Remote HSM Management
The KEES Key Management Team is fully equipped to remotely manage your HSM infrastructure. Leveraging the PCI PTS certified Thales payShield Manager solution from the PCI PIN Certified KEES Service, GEOBRIDGE can remotely manage any Thales HSM environment.
From updating firmware, or adjusting configuration settings, any function organizations would ordinarily employ in their own data center, the GEOBRIDGE KEES Service can augment your staff with subject matter experts to manage this sensitive equipment. With required firmware updates being introduced to the marketplace with greater frequency than ever before, the reliance on a set of untrained volunteers within an organization is no longer a prudent course of action.
Key Escrow
Whether functioning for disaster recovery or legally mandated escrow requirements, any key that has been or is currently used for production purposes must be protected with the same security requirements as a production environment. Most organizations struggle to effectively maintain a full production key inventory, let alone have any degree of confidence in disaster recovery scenarios, that usually remain un-tested. The GEOBRIDGE KEES Service offers a full or partial key inventory escrow capability, fully protected under AES 256 Bit encryption.
Independent of disaster recovery considerations, maintaining a key escrow ensures that an organization is in control of its own keys, without being held captive by any specific manufacturer or technology.
Further, by leveraging a key escrow service, an organization can migrate keys to new wrapping formats such as TR-31, without interrupting production systems.




