UTIMACO - Providing a strong and reliable security solution for Lawful Interception of emails
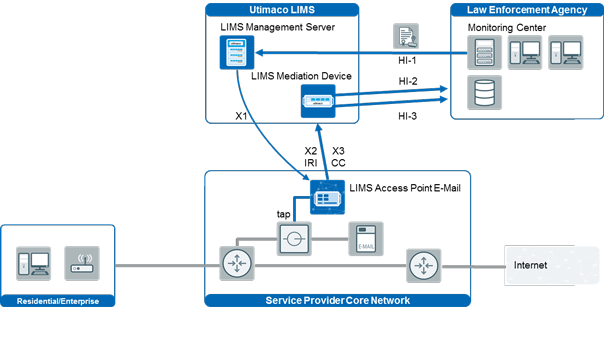
Network probes connected to the core network via taps or switch span-ports (passive interception) are routinely used to intercept email traffic. The probes monitor the entire email traffic of the service provider’ and forward intercepted emails to the LIMS Mediation Device.
Active interception is possible with email servers that provide integrated interception capabilities.
Utimaco provides a proven solution for Lawful Interception of emails in compliance with national laws and international standards, such as ETSI TS 102 232, PacketCable and ATIS T1.678





