In today’s digital age, authenticating users, devices and facilitating the secure electronic transfer of information for a range of industries such as financial services, e-commerce, health, and IoT is an imperative when exchanging data to build trust and secure the business environment.
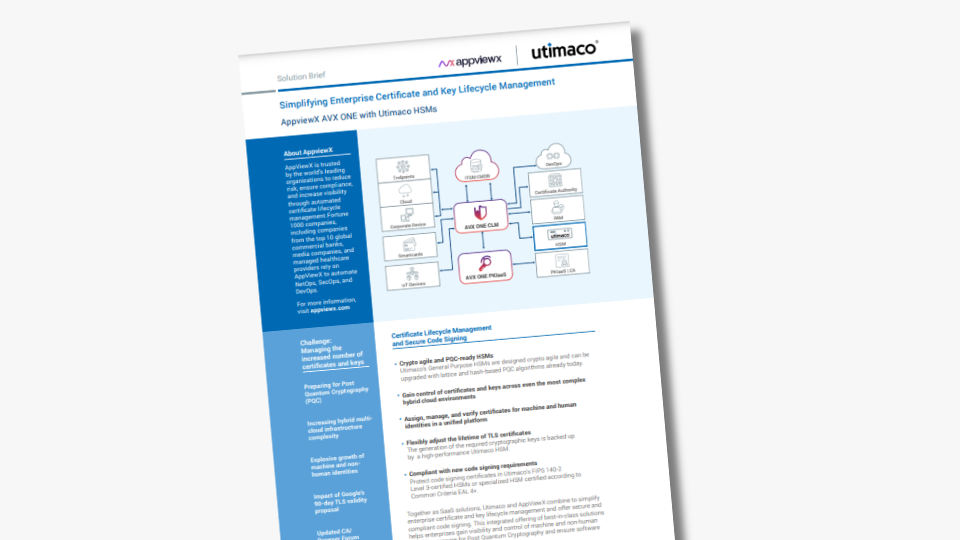
Public key infrastructure (PKI) does this through a framework of cybersecurity and encryption that protects communications between users and website servers. The underlying Hardware Security Module (HSM) is the root of trust which protect PKI from being breached, enabling the creation of keys throughout the PKI lifecycle as well as ensuring scalability of the whole security architecture.
Looking for an HSM that works with your PKI solution?
Download Utimaco’s free HSM simulator for integration testing and validation.

PKI authentication is based on digital certificates and uses encryption and decryption to verify machine and user identities to prove the integrity of digital transactions. With the constant threat of cyber breaches, the ever-growing number of machines used to conduct those transactions must be assured that the information is protected from attacks and can be trusted.
This is when the role of an HSM becomes fundamental – the hardware device that secures all cryptographic processes by generating, managing and protecting the keys used for encrypting and decrypting sensitive data- critical for the information and security for most organizations.
3 Key Components of PKI Authentication
In securing and communicating electronic transactions and digital information, PKI authentication utilizes three key components: digital certificates, certificate authority, and registration authority. These components are hosted on a secure framework so that the PKI can protect identities and private information involved in activities where digital security is needed, including encrypted documents, smart card logins, SSL signatures, etc.
1. Digital Certificates
Digital certificates are at the heart of PKI. They are a form of electronic identification that allows both parties of a transaction to be verified, thus allowing a secure connection between the two. Yes, it is possible for organizations to create their own certificate for internal communications. However, this is not secure enough for external digital transactions. Therefore, PKI digital certificates can be obtained through a Certification Authority (CA), which is a trusted third party issuer.
2. Certificate Authority
The Certificate Authority authenticates users’ digital identities. These identities may range from an individual user, computer system or server. Fraudulent entities are prevented by the CA as the life cycle of the digital certificates are managed in the system. The CA vets the applicants seeking certificates and issues certificates based on their findings.
3. Registration Authority
The Registration Authority (RA) is authorized by the CA to distribute digital certificates on a case-by-case basis to users. All certificates that are requested, received and revoked by both the CA and RA are stored in an encrypted certificate database. A certificate store, which resides on a specific computer, acts as a storage space for all information relevant to a certificate’s history, including private encryption keys and issued certificates.

PKI Performs Encryption
PKI performs encryption through the keys that it generates and uses two different cryptographic keys: a public key and a private key. These keys can be public or private, but they both encrypt and decrypt secure data. Using this two-key encryption system, PKI keeps electronic information secure as it travels between the two parties. Each party is provided with a key to encrypt and decrypt the data.
PKI combines symmetric and asymmetric encryption to protect data:
The symmetric encryption protects the private key generated during the digital handshake (initial exchange) and is passed from one party to the other to allow encryption and decryption of the exchanged information. The private key may be a password, or a random series of numbers or letters generated by a random number generator.
Asymmetric encryption is also known as public key cryptography. It uses two keys, one private and one public. The public key encrypts data while the private key decrypts it. The public key is created for the party sending information to allow them to encrypt the data they are sending. After the second party receives the information, the private key is used to decrypt the information.
How Does Public Key Infrastructure Work?
A PKI can be used for various authentication use cases, We will now explain the flow of a PKI using the example of website authentication:
- The web server sends a request (certificate signing request) to a Registration Authority (RA).
- The RA validates the request and sends it to the Certificate Authority (CA)
- The CA signs the Certificate Signing Request with a private key and bundles it with the public key.
- This way, the certificate is generated which is sent back to the web server.
- The website can now send the certificate to the receiver (browser).
- The browser checks the certificate with the help of a Validation Authority (e.g. a OCSP Responder or a Certificate Revocation List).
- If the certificate is valid, the browser knows that the website is trustworthy.
In this flow, the key pair that is needed for the certificate is generated with an HSM. The private key stays in the secure boundary of the HSM.
PKI Security Only a Piece of the Puzzle
A chain is only as strong as its weakest link. For PKI to protect sensitive digital information as intended, it relies on security and trust. Trust means all cryptographic operations must be conducted in a trust environment that is safe from viruses, malware, exploits and unauthorized access. This is where the HSM comes in.
The hardware security module is a trusted network computer where the cryptographic processes that PKI requires to remain secure and can be used virtually or on a cloud environment. HSMs are designed to protect cryptographic keys and are trusted because they:
- Keep cryptographic material hidden and protected at all times.
- Strengthen encryption practices across the key lifecycle – from key generation through to storage, distribution, back-up and finally, to destruction.
- Provide an additional layer of security by storing the decryption keys separate from the encrypted data, ensuring that even if a data breach occurs, encrypted data is not exposed.
- Are built with specialized, secure hardware, resistant to hacking attempts.
- Have limited access through a strictly controlled network interface.
- Run on a secure operating system.
- Enable scalability and multi tenancy of the security architecture when properly conceived.
- Simplify industry compliance and auditability of the PKI through certified hardware and comfortable audit reporting.
Why do you need an HSM?
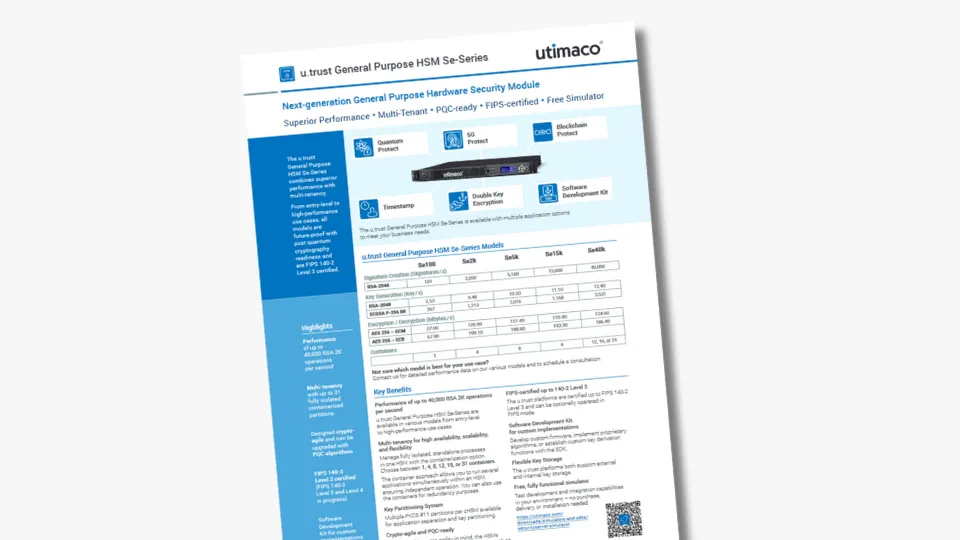
Comparison of performing cryptographic operations in HSMs vs. Software or USB solutions
| HSM | Software Solutions | USB Solutions | |
| Own memory (storage) location | ✔ | x | ✔ |
| Own User Management with dedicated access management | ✔ | ✔| x | ✔| x |
| Both can‘t be captured with a system snapshot | ✔ | x | ✔ |
| Own key management in the hardware | ✔ | x | ✔ |
| Using own True Random Number Generator (TRNG) | ✔ | x | ✔ |
| Whitelisting of authorized applications allowed and able to communicate with the solution | ✔ | ✔| x | ✔| x |
| Keys never leaving the solution unencrypted | ✔ | x | ✔| x |
| Protected against side channel attacks | ✔ | x | ✔| x |
| Firmware and algorithms can just be updated by manufacturer (preventing manipulated firmware and crypto algorithms) | ✔ | ✔| x | ✔| x |
PKI integration testing – download the free HSM simulator
Utimaco offers a free HSM simulator for evaluation and integration testing – the perfect way to check if our HSM meets your requirements: create your HSM simulator account today.
To learn more how HSMs are The Better Choice for Protecting PKI Use Cases, watch out webinar!
Blog post by Dawn Turner from November 2021 – Updated by Lena Franke October 2024