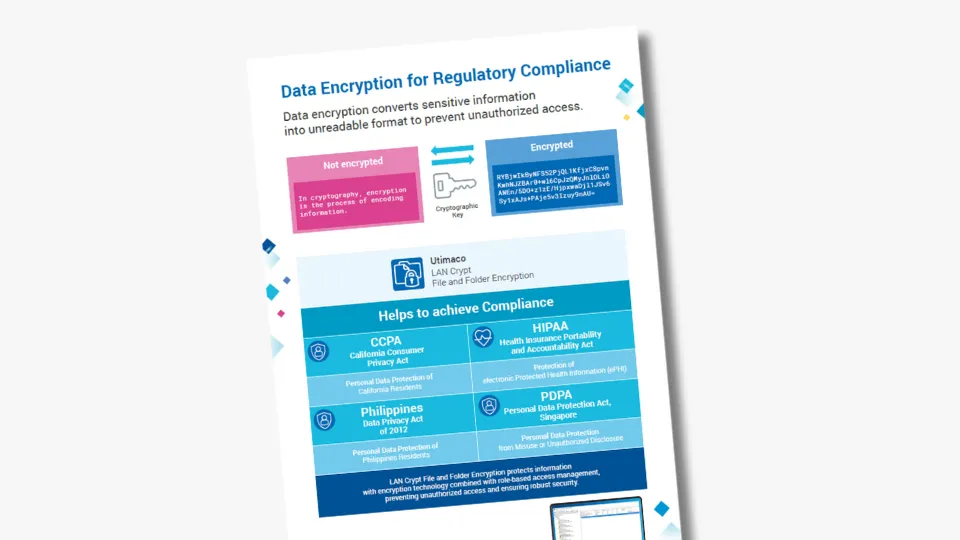
LAN Crypt File and Folder Encryption is an easy-to-install encryption solution that provides an additional layer of data security. With role-based access management, it prevents malicious or unauthorized external access and restricts internal access within organizations ensuring compliant and secure data management.
Available in different versions and deployment options, it ensures that every organization’s encryption needs are reliably fulfilled:
- LAN Crypt 2Go: Allowing secure sharing of external documents with encryption keys managed by the users.
- File and Folder Encryption as a Service: Enabling reliable, role-based data encryption centrally managed in the cloud.
LAN Crypt File and Folder Encryption and LAN Crypt 2Go are also available as VS-NfD-certified version, making it ideal for safeguarding data in classified environments.
Customers have the freedom of choice between on-prem or cloud-hosted administration. Both variants support full key ownership and key custody, ensuring that encryption keys are never exposed to any outside party, as well as the integration with Utimaco’s Enterprise Secure Key Manager for local key storage.