Key management is a cornerstone of modern cybersecurity, ensuring that cryptographic keys are securely stored and managed.
With the variety of use cases and data endpoints, the requirements for a key management system are increasing, further accelerated by the ever increasing threat landscape.
Effective key management is crucial because the strength of an encryption system hinges not only on the algorithms used but also on the protection and management of the keys - make a system as cryptographically strong as you like, and it will still be as accessible as if the keys are not sufficiently protected. On the other hand, Key Management can become a pain if not consolidated in a central management tool enabling transparency throughout the whole crypto key environment.
Learn More About KMS Migration: Watch Our Webinar.

As organizations grow and evolve, so do their key management needs. Migrating to a new key management system (KMS) can offer enhanced security, compliance, and operational efficiency. However, selecting the right vendor for this critical transition can be difficult when there are so many aspects to take into account.
Top Considerations for Choosing a Vendor in KMS Migration
1. Compliance & Security
When it comes to key management, compliance and security are non-negotiable. Your vendor must adhere to the most stringent industry and national compliance standards. Look for certifications required in your specific industry and needed for your individual crypto key use cases to make sure that the vendor's KMS is the right choice for you.
Additionally, the vendor should demonstrate a robust security posture, including strong encryption algorithms, secure key storage mechanisms, and rigorous access controls. This guarantees that your sensitive data remains protected against evolving threats.
2. Agility
The landscape of cryptography is ever-changing, with new algorithms and key management techniques emerging regularly. Your chosen vendor should offer a system that can handle a large volume of keys and support a wide range of cryptographic algorithms, including both current and next-generation standards.
Moreover, the system should be scalable to accommodate future growth and technological advancements. Agility in key management means being prepared for cryptographic advancements, regulatory changes, and business expansion without needing another migration in the near future.
3. On-premises vs. Cloud
Modern networks are often comprised of a mixture of on-premise and cloud-based components, and a Key Management System will need to be equally adept at working in both. Because many companies use more than one cloud environment (Microsoft Azure, Amazon Web Services etc.) the KMS should also be vendor-agnostic, capable of managing keys in multi-cloud or mixed cloud setups.
4. Business Enablement
A key management system should not only secure your cryptographic keys but also enable your business processes. The vendor's solution must integrate smoothly with your existing applications and systems. Look for vendors that offer comprehensive APIs, support for a wide range of cryptographic algorithms, and custom integration capabilities.
Out-of-the-box options for common applications can significantly reduce deployment time and costs. Moreover, the ability to extend the application and customize the system to meet specific business needs is crucial. This ensures that the key management system aligns with your operational workflows and business objectives.
5. Ease of Use & Management
A sophisticated key management system is of little value if it is not user-friendly. The vendor should provide the single pane of glass for all cryptographic keys and their management. This includes - but is not just -an intuitive interface. It also means straightforward key generation, storage, distribution, and rotation processes as well as secure and easy audit log creation.
Learn More About KMS Migration: Watch Our Webinar

Choosing the right vendor for today – and tomorrow’s – challenges
Migrating to a new key management system is a significant undertaking that requires careful planning and consideration. By focusing on compliance and security, agility, deployment options, business enablement, and ease of use, you can select a vendor that not only meets your current needs but also supports your future growth and technological advancements.
Choosing the right vendor is not just about meeting today's requirements but also about preparing for tomorrow's challenges. Make a decision that ensures your organization's cryptographic infrastructure is growing and developing with your business.
If you want to learn more about the most important consideration points for selecting a Key Management solution and best practices for choosing the ideal Key Management solution for your business, listen to our webcast, “Top 5 Considerations for Choosing a Vendor in Key Management System Migration”.
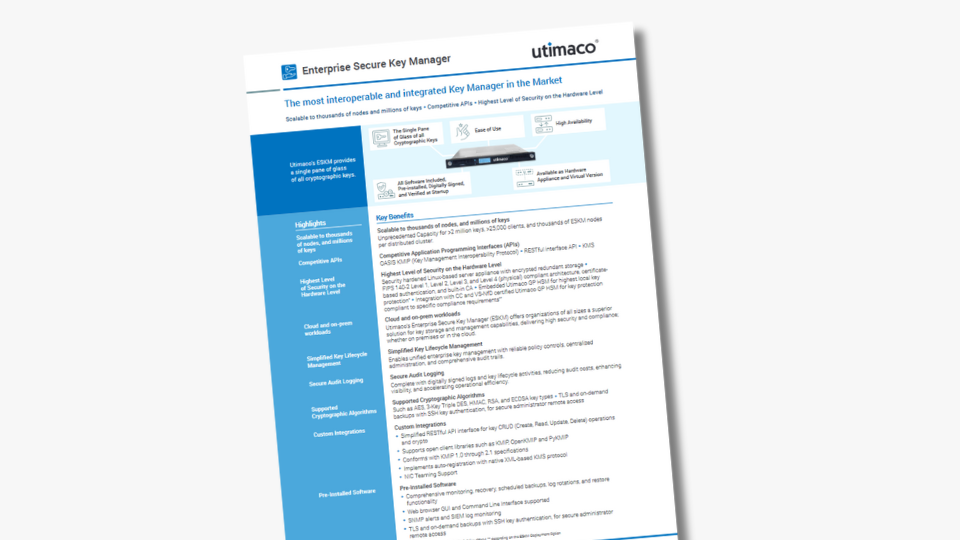
To learn more about Utimaco's unique Key Management offering, download the two-pager data sheet of Enterprise Secure Key Manager.