Security by Design – End-to-end data and IoT devices protection throughout the manufacturing process
Given the interconnected nature of the industry, cyberattacks can be far more extensive than before, and manufacturers and supply networks need to be prepared.
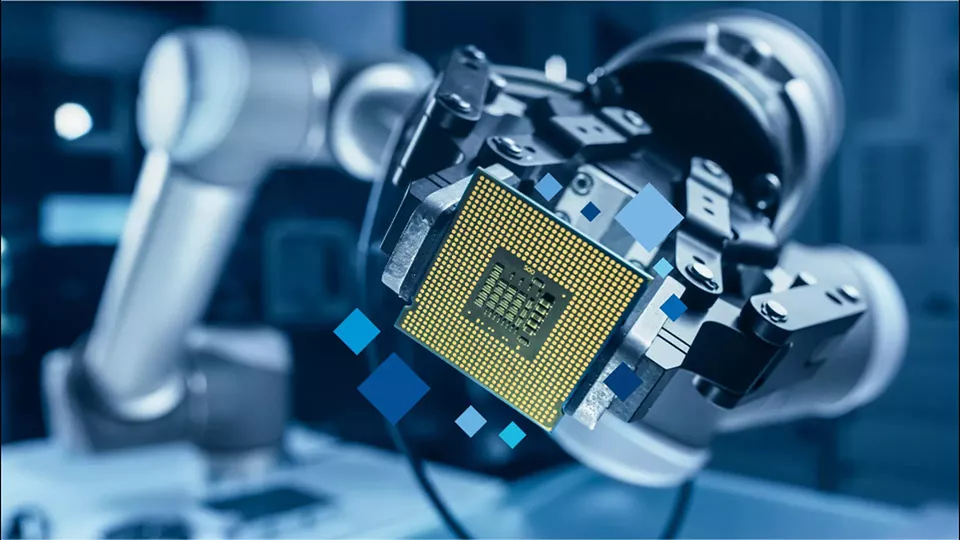
Digital industrial platforms act as both innovation and transaction platforms, allowing for data collection and analysis from various assets and devices. The data or the manufactured products could then be made available to an ecosystem of third-party companies to build consumer or product niches while transforming their manufacturing business model- resulting in further intelligent applications, devices, and services.
End-to-end security in the supply chain indicates not only the protection of data but also the smart tools used to manufacture and the parts and components of manufactured products. Cybersecurity solutions also need to go beyond securing the areas where data is exchanged or the manufacture of smart devices.
A convergence of technologies such as cloud computing, edge computing, big data analytics, and artificial intelligence has resulted in the emergence of digital industrial platforms that drive the advancement of the Industrial Internet of Things (also referred to as Industry 4.0).
Data and IoT devices play a vital role in the transformation of manufacturing processes, although it presents significant challenges in terms of security. Industrial IoT requires a continuous chain of trust that providesadequate levels of security without restricting data exchange, IoT device identity management, and overall identity and access management in manufacturing areas.